IoT Cybersecurity – Boost Your Connected Devices Security
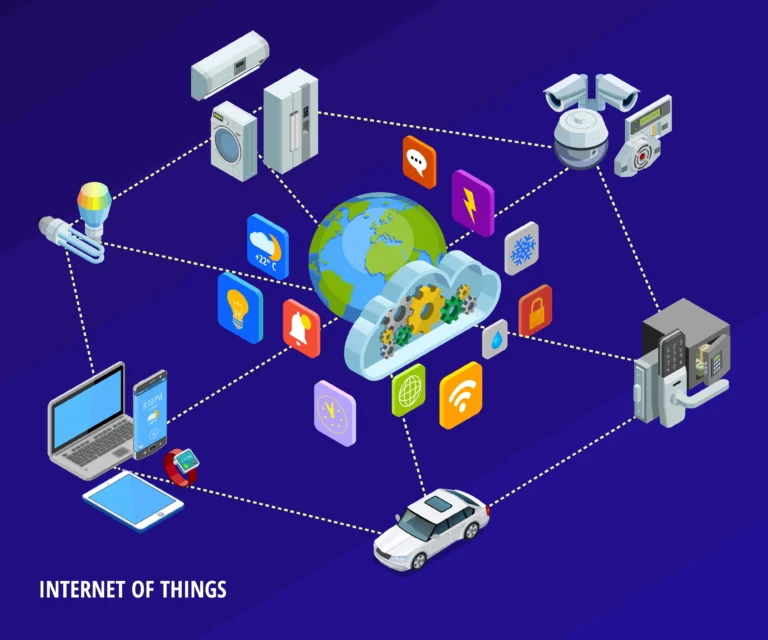
The advent of the Internet of Things (IoT) has revolutionized the way we live and work by interconnecting various devices to the internet. However, with the increase in the number of connected devices, the risk of cyber threats has also escalated. As a result, IoT cybersecurity has become a crucial aspect of protecting IoT devices from unauthorized access, data theft, and other potential vulnerabilities.
Fundamental components of IoT Cybersecurity
The following are the fundamental components of an Internet of Things (IoT) device:
- Firmware: Read-only memory embedded in the device that provides low-level control of the hardware. It can be updated, but usually not programmed. Communicates between each of the elements in the device as well as other networked devices.
- Protective services: A portion of the device’s firmware or operating system that provides security functionality, including the ability to isolate processes so that they can’t be used to defeat security, and encryption.
- Motion sensors: The combined hardware and software used to track the device’s movement. This can include detecting simple movement (e.g., moving the device back and forth, or up and down), or satellite connectivity (e.g., Global Positioning System or GLONASS).
- Microcontroller: The processor used to run the software and provide the “brains” of the unit.
- Connectivity stack: Responsible for providing network connectivity. Networking capabilities can include Bluetooth, mobile (e.g., 3G, 4G, 5G), Zigbee, LoRA, SigFox, or WiFi.
- Authentication services: When included, provides the ability for the IoT device to verify and validate users, network traffic, or processes.
- Power management: If the device requires significant use of power, functionality that manages power usage, as well as the charging of the device.
- Battery/power: The physical capability to store energy, as well as receive power from a remote source.
- Memory: The working “muscle” of the IoT device, in that it provides the ability to store working data, machine code, and information that is then addressed by the processor.
- Storage: Provides the ability to capture and keep data for relatively long periods of time. Such information can include storing the location(s) the IoT device wearer/operator took the device, information about other devices that have connected with it, and information entered by the user. Such information can be added actively (e.g., by the user programming the IoT/OT device on purpose), or passively (e.g., by the device capturing the motions and actions of the wearer/user).
Source: Comptia
How to protect IoT Devices from cyber-attacks?
- To protect IoT devices from cyber threats, it is essential to take proactive measures that can help mitigate the risks. One of the most crucial steps is to ensure that your devices are up-to-date with the latest firmware and software updates. These updates often include critical security patches that can address device vulnerabilities, providing enhanced security and protection against potential cyber threats.
- Another key aspect of IoT cybersecurity is securing your network. You can achieve this by using strong passwords and encryption methods to secure your network access points. Access controls can also be implemented to limit access to IoT devices only to authorized personnel, using role-based access control (RBAC) systems. This can provide an additional layer of security to protect against unauthorized access to sensitive data and systems. It is also critical to monitor network traffic regularly to detect any suspicious activity or potential security breaches. Intrusion detection systems (IDS) and intrusion prevention systems (IPS) can be used to detect, analyze and respond to any suspicious activity in real time. By implementing these systems, you can promptly detect and mitigate any cyber threats before they can cause significant damage.
Why consider Firewalls as IoT Cybersecurity?
Firewalls are another critical component of IoT cybersecurity, which acts as a barrier between your network and the internet. They can monitor and filter network traffic, allowing only authorized access and traffic. By using firewalls, you can ensure that your IoT devices are not exposed to potential threats from the internet, providing an additional layer of security to protect against cyber threats.
As the use of the Internet of Things (IoT) devices continues to rise, it is becoming increasingly important for IT professionals to take steps to ensure their security. Fortunately, there are several technological and personnel solutions available to enhance the security posture of IoT devices.
One effective way to improve the security of IoT devices is to enhance their monitoring. By utilizing an intrusion detection system (IDS) and a security information and event management (SIEM) system, IT professionals can detect and respond to potential security threats more quickly. Additionally, the practice of information sharing can aid in this effort. By using cybersecurity threat intelligence (CTI), it is possible to profile attackers and more intelligently position security controls for IoT and Industrial Control System (ICS) devices.
Another method to bolster the security of IoT devices is to add security features. For example, functionality that encrypts all stored and transmitted data can help to protect sensitive information. Enhanced authentication schemes can also help control connections and prevent unauthorized access. Moreover, workers can be trained to better partition and segment IoT traffic so that it can be easily controlled and managed. This way, they can respond more effectively to any security breaches that may occur.
It is also important to follow established IoT and ICS standards. The National Institute of Standards and Technology (NIST) has published numerous cybersecurity standards, including the Recommendations for IoT Device Manufacturers. Moreover, NIST has provided a helpful page that outlines their Cybersecurity for IoT Program. By adhering to these standards, IT professionals can ensure that their IoT devices are secure and in compliance with industry regulations.
Finally, it is essential to educate yourself and your employees about the risks associated with IoT devices and cybersecurity best practices. This can be achieved through regular training sessions, highlighting the importance of using secure IoT devices, keeping them up-to-date, and following standard cybersecurity practices. By creating awareness and promoting good cybersecurity habits, you can reduce the risk of cyber threats and improve the overall security of your IoT devices.
FAQ
What is IoT cybersecurity?
IoT cybersecurity is the protection of IoT devices and systems from potential cyber threats, including unauthorized access, data theft, and other vulnerabilities.
What are the fundamental components of an IoT device?
The fundamental components of an IoT device include firmware, protective services, motion sensors, microcontrollers, connectivity stack, authentication services, power management, battery/power, memory, and storage.
How can IoT devices be protected from cyber-attacks?
IoT devices can be protected from cyber-attacks by taking proactive measures such as ensuring that devices are up-to-date with the latest firmware and software updates, securing the network with strong passwords and encryption methods, using access controls to limit access to authorized personnel, monitoring network traffic regularly, and implementing firewalls.
What are the benefits of using firewalls for IoT cybersecurity?
Firewalls act as a barrier between your network and the internet, monitoring and filtering network traffic to allow only authorized access and traffic. By using firewalls, you can ensure that your IoT devices are not exposed to potential threats from the internet, providing an additional layer of security to protect against cyber threats.
What are some methods to enhance the security of IoT devices?
Methods to enhance the security of IoT devices include enhancing monitoring by utilizing an intrusion detection system (IDS) and a security information and event management (SIEM) system, adding security features such as encryption and authentication schemes, following established IoT and ICS standards, and educating yourself and your employees about the risks associated with IoT devices and cybersecurity best practices.